

The cloud has given its users enormous resilience, benefit and agility. But what happens when the cloud gets attacked? Recent incidents of data breaches affecting some of the world’s biggest brand names stand as evidence that the cloud remains vulnerable. According to recent data by security experts, 53% of companies today are concerned about the security of Kubernetes. It is estimated that cyberattacks in the cloud have increased by 56% over the past year.
So, while there is an appreciation for the benefits of microservices, docker, and containers for their ability to deliver software at the speed of business, if an organization relying on this technology is not careful, it can increase its attack surface, and its vulnerability to threat.
AccuKnox was founded in the fall of 2020 to simplify the process of securing enterprise workloads against software supply chain issues, vulnerabilities, misconfigurations and malicious adversaries.
“Almost any kind of security threat can be divided into two types. There are problems with a known signature and unknown problems where there is no signature. In other words, no one has ever seen it before. To address those security risks you need a different set of sophisticated controls and mechanisms. Legacy and non-cloud-native security tools add complexity, costs and delays. So that is the problem we set out to solve,” explains Nat Natraj, CEO, AccuKnox.
 He explains that AccuKnox simplifies the process, from development to runtime by providing deep security observability into application behavior, automating zero trust policy management, continuous monitoring and compliance and anomalous behavior detection.
He explains that AccuKnox simplifies the process, from development to runtime by providing deep security observability into application behavior, automating zero trust policy management, continuous monitoring and compliance and anomalous behavior detection.
At the helm of AccuKnox is Co-Founder and Chief Scientists Phil Porras, who is also Program Director of the Internet Security Research in Stanford Research Institute (SRI) International's Computer Science Laboratory, and an SRI Fellow. As an established and active researcher in the field of Computer and Network Security, Porras’ expertise in intrusion detection, alarm correlation, malware analysis, dark web and social media analysis, cloud security, active and software-defined networks, 5G security, and wireless security is globally recognized and was instrumental in informing AccuKnox’s approach to market.
Given the complexity of the problem presented by zero-day attacks where there is no signature, the team at AccuKnox wanted to engage the world’s most brilliant programming minds to help solve it. So the company launched its first product, KubeArmor, as an open-source CNCF project.
“We knew that hard problems require more than just one group of people,” says Nat. “You need a whole community behind it. As such, KubeArmor was adopted and enriched by the community. And today, it has reached 500,000 downloads, tracking to about 50,000 new downloads a month. It has become the bedrock foundation upon which our enterprise solution was built.”
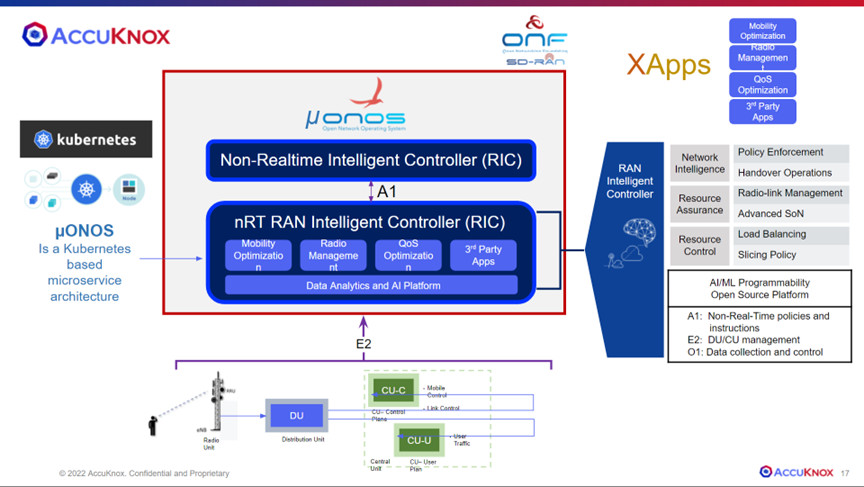
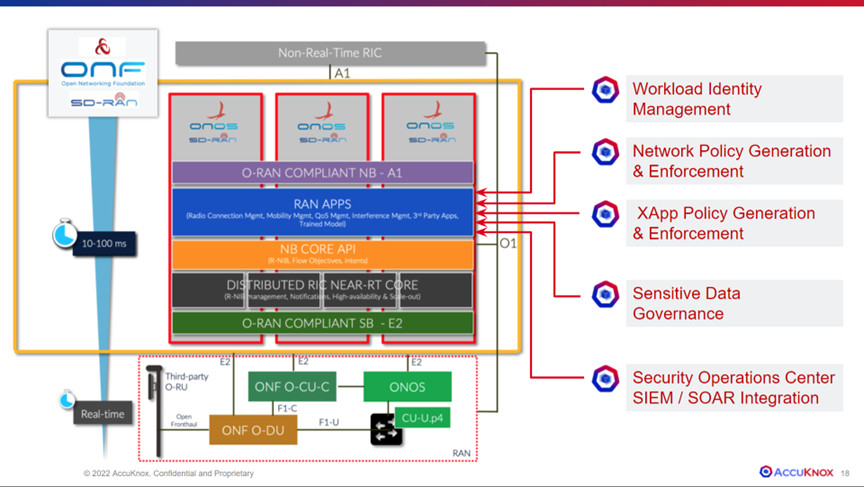
The AccuKnox platform can be used by enterprises to monitor and protect workloads however and wherever they run, including in Containers, Kubernetes, virtual machines, or bare metal. AccuKnox also operates in private, public, hybrid cloud, edge or IoT, or even within a 5G infrastructure.
Zero Trust Runtime Security:
AccuKnox automates the process of application hardening & firewalling for cloud-native applications to help users achieve Zero Trust/Least Privilege Security. The company’s unique application insights and automated policy discovery engines greatly simplify the work required to analyze applications and create effective security policies.
Security Observability:
AccuKnox can be used by enterprises to understand what applications - including embedded dependencies - are doing and gather insights into runtime behavior and process execution, forking, network and file access. This allows users to detect changes and risky behavior in the software supply chain from development to, staging to production.
Network Segmentation and Firewalling:
Kubernetes pods and services in different namespaces can still communicate with each other unless additional separation is enforced. Manually configuring network and firewall policies is time-consuming and error-prone. AccuKnox automatically analyzes applications behavior and creates least privilege network policies to be implemented by existing, high-performance linux security modules. This means network policies move as code with the application, greatly increasing the speed, control and confidence of DevSecOps teams.
Continuous Compliance:
Assess & demonstrate compliance with regulatory standards like PCI & NIST. Implement policies in Audit mode to continuously monitor the workloads for deviations from NIST, PCI and other standards. Get high-value, actionable alerts for your SecOps team – or enforce Runtime Security and implement guard rails for risky behavior.
Anomaly Detection:
AccuKnox implements Anomaly Detection using Variational Autoencoder (VAE) technology developed in partnership with SRI to help enterprises detect and protect against anomalous and malicious behavior including policy drive and ‘unknown unknowns.”. Variation Autoencoding is a deep learning algorithm that uses dual conversational neural networks to analyze activity patterns for anomalous behavior. It has been tested successfully against a number of Zero Day threats like crypto jacking, HTTP flood attacks, etc.
Vulnerability Scanning:
The NSA and CISA Kubernetes hardening guide recommends scanning containers and pods for vulnerabilities or misconfigurations. AccuKnox helps enterprises reduce the risk of critical vulnerabilities by identifying known vulnerabilities in images and pods before they are released into production and by implementing monitoring, image assurance and runtime security policies to protect them.
Advanced Cloud Workload Protection:
AccuKnox helps enterprises protect applications, data and the network by providing a unified policy framework for protecting cloud workloads. This includes identity, application, data and network components that span kernel system calls up to layer 7 API access, giving DevSecOps teams extremely fine granularity over the guard rails that can be put in place – as well as the auditing specifications.
AccuKnox and 5G Open Innovation Labs:
AccuKnox joined 5G Open Innovation Labs as part of the Lab’s most recent batch 6 group of startups in September of 2022. Through recent funding from SRI, the National Science Foundation and Ohio State University AccuKnox has been actively working on a solution to deliver zero trust for organizations implementing public 5G networks.
“From educational and healthcare campuses to mining and public utility operations to the military, the demand for 5G-enabled private networks is growing exponentially. But with that come some significant security concerns,” says Nat. “With respect to data traffic, the question becomes, what is allowed? The answer is not to deny, because that would mean denying everything. Therefore, it becomes about what kind of traffic can be whitelisted. Our Zero Trust Platform gives enterprises the tools they need to examine and control high volumes, variety and velocity traffic in a highly managed and very efficient way. And our alliance with 5G Open Innovation Labs opens up to us an entire industry ecosystem to support our go-to-market efforts.
Posted May 17, 2023